Phishing Email Templates
Phishing Email Templates - One has a bunch of phishing email templates to be used with gophish. This would be the email folder. Phishing simulations provides standard simulation email templates with different languages, difficulty levels, and target audiences. Our phishing simulation templates are created with the. Here are our top 10 phishing email templates. These email templates have some of the highest compromise rates we've seen within our customers' phishing simulation reports, as well as some of the most common techniques used. A library of free phishing email templates themed against popular tools, services, and platforms. This email is incredibly effective and borderline lethal around the. Use them with great responsibility. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. One has a bunch of phishing email templates to be used with gophish. This month, we're unveiling five chilling phishing simulation scenarios that exploit. Use them with great responsibility. A library of free phishing email templates themed against popular tools, services, and platforms. Phishing simulations provides standard simulation email templates with different languages, difficulty levels, and target audiences. With email phishing being rampant nowadays, here are phishing email examples for training your. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. By using different types of email templates, you can create realistic scenarios that help. Here are our top 10 phishing email templates. These email templates have some of the highest compromise rates we've seen within our customers' phishing simulation reports, as well as some of the most common techniques used. Our phishing simulation templates are created with the. This email is incredibly effective and borderline lethal around the. A library of free phishing email templates themed against popular tools, services, and platforms. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. Use them with great responsibility. You can also create your own simulation email template. A library of free phishing email templates themed against popular tools, services, and platforms. Use them with great responsibility. This month, we're unveiling five chilling phishing simulation scenarios that exploit. Our phishing simulation templates are created with the. Get these emails as a free pdf. Emails can be modified to include custom company information or sent as is. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. You can also create your own simulation email template. With email phishing being rampant nowadays, here are phishing. Here are our top 10 phishing email templates. Emails can be modified to include custom company information or sent as is. Employees are the weakest link to an organisation's cybersecurity. By using different types of email templates, you can create realistic scenarios that help. Phishing simulations provides standard simulation email templates with different languages, difficulty levels, and target audiences. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. Our phishing template library offers the right message, at the right time, in virtually any language, for every target in your organization. This would be the email folder. Emails can be modified to include custom company information or. Emails can be modified to include custom company information or sent as is. Our phishing template library offers the right message, at the right time, in virtually any language, for every target in your organization. This month, we're unveiling five chilling phishing simulation scenarios that exploit. Phishing simulations provides standard simulation email templates with different languages, difficulty levels, and target. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. This would be the email folder. One has a bunch of phishing email templates to be used with gophish. Get these emails as a free pdf. Our phishing simulation templates are created with the. This month, we're unveiling five chilling phishing simulation scenarios that exploit. Here are our top 10 phishing email templates. Use them with great responsibility. This email is incredibly effective and borderline lethal around the. Emails can be modified to include custom company information or sent as is. This email is incredibly effective and borderline lethal around the. By using different types of email templates, you can create realistic scenarios that help. Phishing simulation emails are a fantastic way to train your team to recognize and avoid cyber threats. Employees are the weakest link to an organisation's cybersecurity. This would be the email folder. You can also create your own simulation email template. Our phishing simulation templates are created with the. This month, we're unveiling five chilling phishing simulation scenarios that exploit. One has a bunch of phishing email templates to be used with gophish. This email is incredibly effective and borderline lethal around the. Emails can be modified to include custom company information or sent as is. Get these emails as a free pdf. This month, we're unveiling five chilling phishing simulation scenarios that exploit. You can also create your own simulation email template. Our phishing template library offers the right message, at the right time, in virtually any language, for every target in your organization. By using different types of email templates, you can create realistic scenarios that help. Phishing simulations provides standard simulation email templates with different languages, difficulty levels, and target audiences. Here are our top 10 phishing email templates. One has a bunch of phishing email templates to be used with gophish. With email phishing being rampant nowadays, here are phishing email examples for training your. Phishing simulation emails are a fantastic way to train your team to recognize and avoid cyber threats. Here, we've assembled ten sample phishing email templates tailored to gauge the susceptibility of individuals within your organization to actual phishing attacks. This email is incredibly effective and borderline lethal around the. Our phishing simulation templates are created with the. These email templates have some of the highest compromise rates we've seen within our customers' phishing simulation reports, as well as some of the most common techniques used.20 types of phishing attacks + phishing examples Norton
Día mundial de las redes sociales Qué es el phishing y cómo evitarlo
Phishing y pharming ¿qué son y cómo se diferencian? Espacios Net
Qué es el phishing una guía para detectarlo InnovaciónDigital360
Phishing qué es y cómo evitarlo ¡Identifica una de las técnicas
How to prevent phishing attacks 8 signs of a scam email
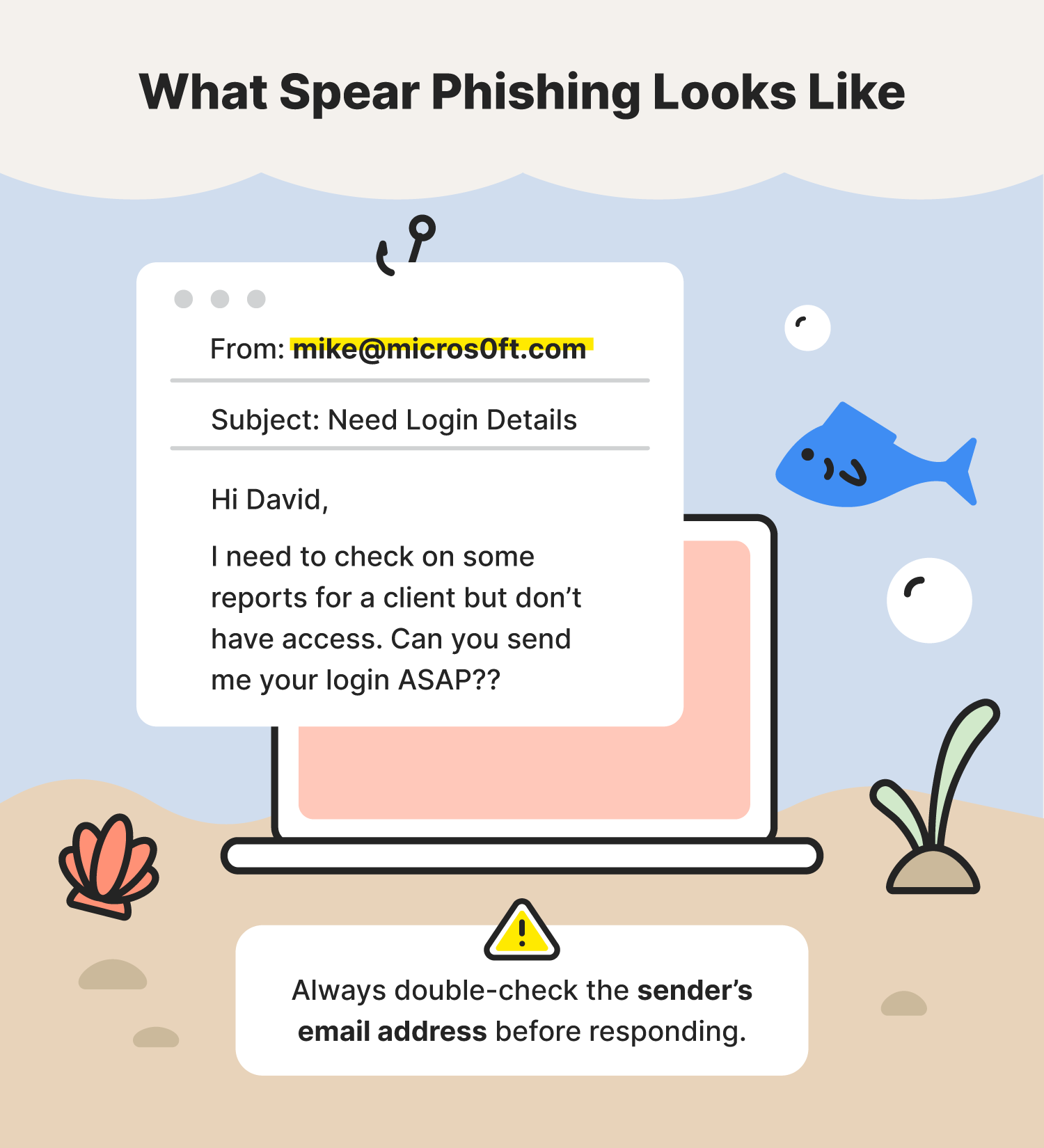
20 types of phishing attacks + phishing examples Norton
¿Qué es el Phishing? Conoce los tipos que existen y aprende a protegerte
15 Types of Phishing and How To Protect Your Business Graphus
¿Qué es el phishing y cómo evitarlo? GVAD
Use Them With Great Responsibility.
Employees Are The Weakest Link To An Organisation's Cybersecurity.
This Would Be The Email Folder.
A Library Of Free Phishing Email Templates Themed Against Popular Tools, Services, And Platforms.
Related Post: